The dangers of public Wi-Fi
Remote working is on the rise
Working from home used to mean an unofficial day off, but it’s becoming an increasingly common way for people to – well, actually work. For these people, pitching up at a coffee shop is not unusual. Lots of people do it. They're no longer the reserve for would-be screenwriters. There are numerous benefits, such as easy access to overpriced coffees and the option to be sociable but with no obligation to actually be so. You also have access to all the free Wi-Fi you can fill your pockets with. However, as is often the case, the idea is better than the reality.
Public Wi-Fi can be a tricky beast and you should always treat it with suspicion. The problem is that it’s public, and therefore anyone can get involved. It only takes one person to ruin it for the rest of us. To keep your data and your identity safe online, you must assume there are plenty of those ruiners lurking about.
Traditional security best practices warn against doing things like signing into your online banking on public Wi-Fi. Whilst it’s definitely better to do this on your mobile data or when connected to your home Wi-Fi, anything sent over HTTPS is theoretically encrypted and most reputable banks have measures in place such as memorable information or 2FA, which means your banking at least is relatively safe. If you’re not using a reputable bank, well, public Wi-Fi is probably the least of your worries. However, there certainly are risks to bear in mind when using public Wi-Fi. Let’s look at some.
Public Wi-Fi can be a tricky beast and you should always treat them with suspicion.
Man-in-the-middle attack
A common threat when using public Wi-Fi is that anyone else who happens to be sitting on the network can potentially see what you’re up to. Open networks that require no authentication to access are a hacker’s favourite. All they have to do is sit between you and the endpoint. Once there, they can intercept traffic and rifle through an endless stream of your data. Sending and receiving work emails or sorting out some personal finances suddenly seems a lot riskier.
Any information you send out can be intercepted by a man in the middle before it’s sent on. This can include security credentials to your business network, putting more than just your computer and your information at risk.
Even if it’s seemingly inconsequential information, such as the apps used, an email address or a preferred username, the information is useful for social engineering.

Using a laptop in a public place? You might not be the only one reading your emails.
Wi-Fi encryption
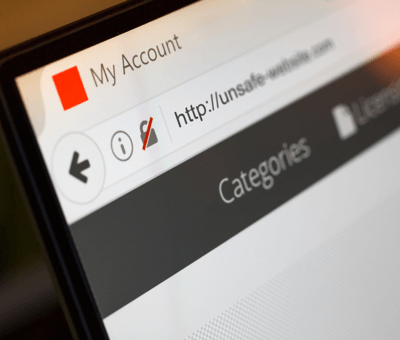
No green padlock? Think twice about using these sites insecure website connections.
As mentioned before, a great deal of the data leaving your device will be encrypted, meaning those nefarious middlemen won’t be able to do much with what they get. However, not all encryption is created equal and not everything is encrypted. In recent years there has been much ado about HTTPS and how much better it is than HTTP, and that has pushed the majority of sites to use it. However, not every site does.
If you are like me, you have every single app running in the background on your phone (and constantly question why your battery drains so quickly), it’s likely that these are set up to check in with their servers every once in a while. If they’re doing that on public networks, then any data they send out can be gobbled up too. Again, this data is often encrypted, but every app is different with many not being built with security in mind. Just ask some of our penetration testers. Man-in-the-middle attacks are so easy to execute on public Wi-Fi that the risks outweigh the benefit.
Let’s not forget that there are various levels of encryption. Over the years we’ve seen new versions of TLS emerge, meaning there have been weaknesses in the cryptography used previously. There’s nothing to say that app developers have kept their security implementation up to date, nor that someone will find a way to crack whatever the latest encryption standard is in the future.
Man-in-the-middle attacks are so easy to execute on public Wi-Fi that the risks outweigh the benefit.
Shoulder surfing
Another process hackers often employ is one I have used myself on occasion when the person in front of me on the bus is reading a good book. Shoulder surfing is indeed a danger when working on public Wi-Fi. All sorts of information can be gleaned from a casual or not-so-casual glance. These wandering eyes can soak up logins and other pieces of sensitive information and potentially log into your accounts. Or, they can see what sites you browse and log into, potentially your username (maybe even your email) and they have some information to do some brute forcing with or craft a more convincing phishing email.
Risks of file sharing
Sharing is a wonderful trait. If only we were all willing to share more – the world would be a much better place. Having said that, it’s not necessarily true with file sharing. It might make things easier in the office or at home, providing everyone with those important financial docs or holiday photos. However, on a public Wi-Fi, you could be unwittingly handing them out to any Tom, Dick or Norbert. Not only could hackers be intercepting the data you send out, with filesharing switched on, they could be rummaging through your files too. Along with the obvious files a hacker might be after (such as anything financial), don’t forget the personal touch. Your file sharing would also leave lots of personal data vulnerable for a hacker to commit a spot of identity theft.
Alternatively, a hacker could set up their own file, load it with malware and wait for people to stumble upon it. Curiosity often gets the better of people when they see an odd folder they don’t realise isn’t theirs. Especially if that folder is called ‘Interesting things you should look at right now’.
 File sharing, doesn’t necessarily always look as fancy as this...
File sharing, doesn’t necessarily always look as fancy as this...
Once you’ve inadvertently installed malware onto your machine, hackers can then compromise other networks you choose to connect to, and any machine connected to them. Next time you take that laptop into work, congratulations, you’ve just compromised your work network too.
The convenience factor of public Wi-Fi is impossible to dismiss, but you definitely need to take precautions.
Endpoint attacks
 Your network is only as secure as the least secure device.
Your network is only as secure as the least secure device.
Endpoint attacks are common in any network, but more so on a public one. An endpoint is any internet capable device on a network, be it a desktop, laptop, phone or tablet. Any one of these can provide entry to a network. In a business environment, most endpoints will have been built to a specification which hopefully adheres to security best practices. If they aren’t in your business, start doing that. Even so, not everyone diligently installs their updates. If you operate on a BYOD policy, you could be at a greater risk, not everyone’s computer will be as secure or as up to date. If you’re on a public Wi-Fi, you’re at the mercy of everyone’s lax security approach.
Compromising one endpoint can be done in a number of ways, for example, a hacker could set up a malicious website that users browse to, thus letting them in. If they’ve set up their own rogue access point (see below), then they can forcibly direct everyone to the malicious website at their leisure. If someone else sitting on the network gets hacked, then said hacker potentially has access to every device on it, including yours.
It’s worth noting that if your machine is compromised, any site that you have set to ‘remember your credentials’ may well be visible to the hacker. This could lead to them accessing personal information and even potential credit card info. It will also allow them to craft some fairly convincing phishing emails.
Rogue access points
Rogue access points (AP) are a worry. They can exist in any network environment. There could even be one in your office, set up by a well-meaning but knowledge-lacking employee.
A rogue AP can also be a compromised router or one that has been deliberately installed by a hacker. In some cases, this can allow hackers to run vulnerability scans or sniff packets and nab passwords and financial information and the like. They can even push malware out to computers that connect to it. Depending on what this malware is, you might find hackers can start pilfering all your secrets.

Think twice before connecting to an open wifi network.
The convenience factor of public Wi-Fi is impossible to dismiss, but you definitely need to take precautions.
Protecting your Wi-Fi connection

A VPN is a good step in the right direction to keeping your data secure.
So, should you avoid using public Wi-Fi? The convenience factor of public Wi-Fi is impossible to dismiss, but you definitely need to take precautions. Public Wi-Fi is susceptible to the same threats as any other network, only they’re much more vulnerable to them. Mostly, it comes down to not knowing who set them up or who’s connected to them. Infected devices and man in the middle attacks are more likely to cause havoc on public networks than private ones. Ensure your phone and laptop are kept updated and that your firewall is appropriately configured. Be careful what apps you're using and make sure the sites you visit are HTTPS.
It's at this point one might recommend using a secure VPN to add an extra layer of security to your communications, but even this is no sure thing if the public network itself is already compromised. Still, take every precaution you can. Public Wi-Fi is great and isn’t going anywhere. If you are going to use them, and you probably are, be on top of your cyber security.

Protect your network
Worried about remote workers on public Wi-Fi? Let Bulletproof conduct a vulnerability scan across all your devices.
Learn moreRelated resources
Get a quote today
If you are interested in our services, get a free, no obligation quote today by filling out the form below.