Raspberry Pi and Linux Machines top target for default credential hacking
Research reveals the extent of hackers using default credentials to target businesses.
Stevenage, 15th March 2022 – Today new findings from the Bulletproof Annual Cyber Security Industry Threat report highlight the issue posed by poor security hygiene as automated attacks remain a high security threat to businesses. The research gathered throughout 2021, showed that 70% of total web activity is currently bot traffic. With hackers increasingly deploying automated attack methods, Bulletproof revealed that default credentials are the most common passwords used by these bad actors, acting in effect as a ‘skeleton key’ for criminal access.
Bulletproof’s SOC team undertook the research by running servers in public cloud environments with deliberate security vulnerabilities, known as honeypots. This enabled them to gather intelligence on hackers’ behaviours and tactics.
Password hygiene remains a critical issue
The research revealed that hackers are consistently using, and gaining access to servers, with the same regular passwords. Some of these are default passwords that have not been changed since entering into use by the business.
The top failed login attempts on our honeypot servers were using the following credentials:
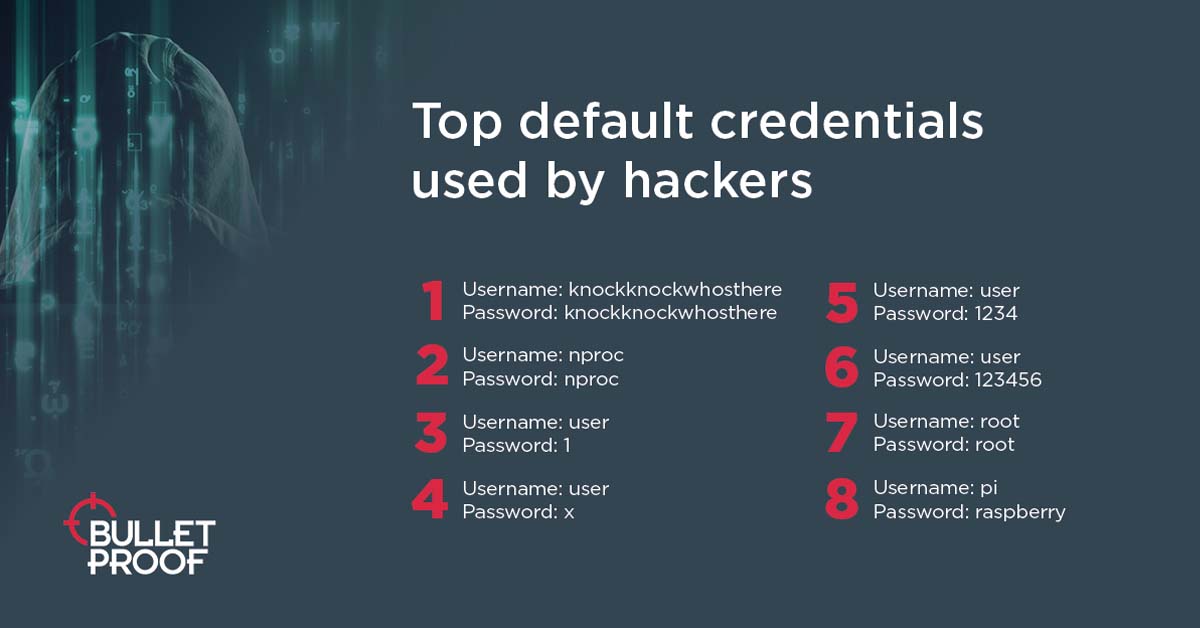
"On the list are the default Raspberry Pi credentials (un:pi/pwd:raspberry). There are more than 200,000 machines on the internet running the standard Raspberry Pi OS, making it a reasonable target for bad actors. We also can see what looks like credentials used on Linux machines (un:nproc/pwd:nproc). This highlights a key issue – default credentials are still not being changed, said Brian Wagner, Chief Technology Officer at Bulletproof. Using default credentials provides one of the easiest entry points for attackers, acting as a ‘skeleton key’ for multiple hacks. Using legitimate credentials can allow hackers to avoid detection and makes investigating and monitoring attacks much harder.
A quarter of the passwords used by attackers today originate from the RockYou database leak from December 2009. This level of activity indicates that these passwords remain viable. Bulletproof’s own penetration testers also attempt to use these passwords during testing as they still have such a high success rate.
Top passwords used as part of brute-force attacks:

More than 240k sessions
Over the course of the research, bad actors initiated more than 240,000 sessions. The top IP address, which connected from a German server, initiated over 915 sessions and spent a total of five hours on the Bulletproof honeypot. Another attacker spent 15 hours on the honeypot, logging in successfully 29 times with over 30 unique passwords.
In total, 54% of over 5,000 unique IP addresses had intelligence that suggested they were bad actor IP addresses.
Within milliseconds of a server being put on the internet, it is already being scanned by all manner of entities. Botnets will be targeting it and a host of malicious traffic is then being driven to the server, continued Wagner.Although some of our data shows legitimate research companies scanning the internet, the greatest proportion of traffic we encountered to our honeypot came from threat actors and compromised hosts.
These insights, combined with our data, highlight the importance of proactive monitoring to ensure you are aware of the threats to your business on a daily basis, as well as a tried and tested incident response plan."

Related resources
Get a quote today
If you are interested in our services, get a free, no obligation quote today by filling out the form below.













